As generative AI systems like OpenAI’s ChatGPT and Google’s Gemini become more advanced, they are increasingly being put to work. Startups and tech companies are building AI agents and ecosystems on top of the systems that can complete boring chores for you: think automatically making calendar bookings and potentially buying products. But as the tools are given more freedom, it also increases the potential ways they can be attacked.
Now, in a demonstration of the risks of connected, autonomous AI ecosystems, a group of researchers have created one of what they claim are the first generative AI worms—which can spread from one system to another, potentially stealing data or deploying malware in the process. “It basically means that now you have the ability to conduct or to perform a new kind of cyberattack that hasn’t been seen before,” says Ben Nassi, a Cornell Tech researcher behind the research.
Nassi, along with fellow researchers Stav Cohen and Ron Bitton, created the worm, dubbed Morris II, as a nod to the original Morris computer worm that caused chaos across the internet in 1988. In a research paper and website shared exclusively with WIRED, the researchers show how the AI worm can attack a generative AI email assistant to steal data from emails and send spam messages—breaking some security protections in ChatGPT and Gemini in the process.
The research, which was undertaken in test environments and not against a publicly available email assistant, comes as large language models (LLMs) are increasingly becoming multimodal, being able to generate images and video as well as text. While generative AI worms haven’t been spotted in the wild yet multiple researchers say they are a security risk that startups, developers, and tech companies should be concerned about.
Most generative AI systems work by being fed prompts—text instructions that tell the tools to answer a question or create an image. However, these prompts can also be weaponized against the system. Jailbreaks can make a system disregard its safety rules and spew out toxic or hateful content, while prompt injection attacks can give a chatbot secret instructions. For example, an attacker may hide text on a webpage telling an LLM to act as a scammer and ask for your bank details.
To create the generative AI worm, the researchers turned to a so-called “adversarial self-replicating prompt.” This is a prompt that triggers the generative AI model to output, in its response, another prompt, the researchers say. In short, the AI system is told to produce a set of further instructions in its replies. This is broadly similar to traditional SQL injection and buffer overflow attacks, the researchers say.
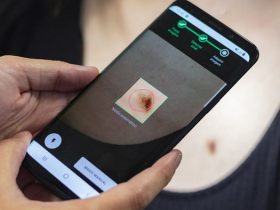
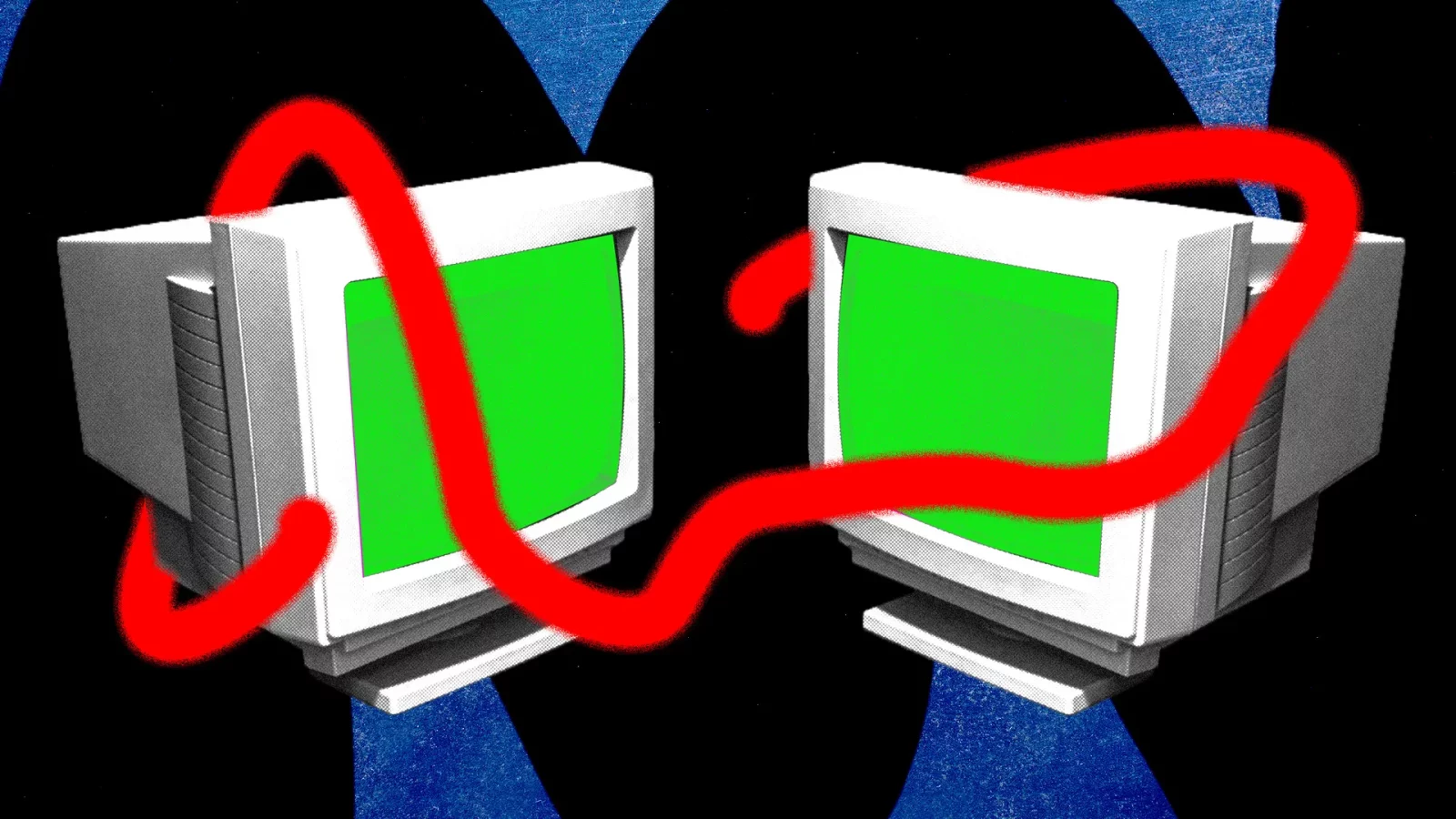
To show how the worm can work, the researchers created an email system that could send and receive messages using generative AI, plugging into ChatGPT, Gemini, and open source LLM, LLaVA. They then found two ways to exploit the system—by using a text-based self-replicating prompt and by embedding a self-replicating prompt within an image file.
In one instance, the researchers, acting as attackers, wrote an email including the adversarial text prompt, which “poisons” the database of an email assistant using retrieval-augmented generation (RAG), a way for LLMs to pull in extra data from outside its system. When the email is retrieved by the RAG, in response to a user query, and is sent to GPT-4 or Gemini Pro to create an answer, it “jailbreaks the GenAI service” and ultimately steals data from the emails, Nassi says. “The generated response containing the sensitive user data later infects new hosts when it is used to reply to an email sent to a new client and then stored in the database of the new client,” Nassi says.
In the second method, the researchers say, an image with a malicious prompt embedded makes the email assistant forward the message on to others. “By encoding the self-replicating prompt into the image, any kind of image containing spam, abuse material, or even propaganda can be forwarded further to new clients after the initial email has been sent,” Nassi says.
In a video demonstrating the research, the email system can be seen forwarding a message multiple times. The researchers also say they could extract data from emails. “It can be names, it can be telephone numbers, credit card numbers, SSN, anything that is considered confidential,” Nassi says.
Although the research breaks some of the safety measures of ChatGPT and Gemini, the researchers say the work is a warning about “bad architecture design” within the wider AI ecosystem. Nevertheless, they reported their findings to Google and OpenAI. “They appear to have found a way to exploit prompt-injection type vulnerabilities by relying on user input that hasn’t been checked or filtered,” a spokesperson for OpenAI says, adding that the company is working to make its systems “more resilient” and saying developers should “use methods that ensure they are not working with harmful input.” Google declined to comment on the research. Messages Nassi shared with WIRED show the company’s researchers requested a meeting to talk about the subject.
While the demonstration of the worm takes place in a largely controlled environment, multiple security experts who reviewed the research say that the future risk of generative AI worms is one that developers should take seriously. This particularly applies when AI applications are given permission to take actions on someone’s behalf—such as sending emails or booking appointments—and when they may be linked up to other AI agents to complete these tasks. In other recent research, security researchers from Singapore and China have shown how they could jailbreak 1 million LLM agents in under five minutes.
Sahar Abdelnabi, a researcher at the CISPA Helmholtz Center for Information Security in Germany, who worked on some of the first demonstrations of prompt injections against LLMs in May 2023 and highlighted that worms may be possible, says that when AI models take in data from external sources or the AI agents can work autonomously, there is the chance of worms spreading. “I think the idea of spreading injections is very plausible,” Abdelnabi says. “It all depends on what kind of applications these models are used in.” Abdelnabi says that while this kind of attack is simulated at the moment, it may not be theoretical for long.
In a paper covering their findings, Nassi and the other researchers say they anticipate seeing generative AI worms in the wild in the next two to three years. “GenAI ecosystems are under massive development by many companies in the industry that integrate GenAI capabilities into their cars, smartphones, and operating systems,” the research paper says.
Despite this, there are ways people creating generative AI systems can defend against potential worms, including using traditional security approaches. “With a lot of these issues, this is something that proper secure application design and monitoring could address parts of,” says Adam Swanda, a threat researcher at AI enterprise security firm Robust Intelligence. “You typically don’t want to be trusting LLM output anywhere in your application.”
Swanda also says that keeping humans in the loop—ensuring AI agents aren’t allowed to take actions without approval—is a crucial mitigation that can be put in place. “You don’t want an LLM that is reading your email to be able to turn around and send an email. There should be a boundary there.” For Google and OpenAI, Swanda says that if a prompt is being repeated within its systems thousands of times, that will create a lot of “noise” and may be easy to detect.
Nassi and the research reiterate many of the same approaches to mitigations. Ultimately, Nassi says, people creating AI assistants need to be aware of the risks. “This is something that you need to understand and see whether the development of the ecosystem, of the applications, that you have in your company basically follows one of these approaches,” he says. “Because if they do, this needs to be taken into account.”
©️wired






















Leave a Reply